1. What is Deployment Policy?
An object in Datapower used to modify/filter imported configurations. When we import object(s) from one domain or environment to another, we may want to filter out or change certain object configurations for the new domain or environment. This can be achieved using (DP)Deployment Policy.
2. How does DP work?
Deployment Policy works through rules. A DP may contain three types of rules-
a) Accepted Configuration - Only the matching configuration is accepted during import.
b) Filtered Configuration - The matching configuration is excluded during import.
c) Modified Configuration - The matching configuration is altered during import.
3. Describe configuration of Deployment policy along with each type of rule mentioned above.
To create a DP, follow the below steps:
To create a DP, follow the below steps:
i) In the left search panel in Datapower, type Deployment Policy .
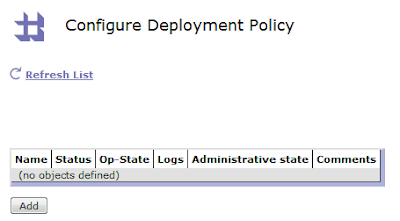
ii) The below window opens. Go to Add.
iii) In the Main tab, enter a name for the Deployment Policy. Write comment (optional) for this DP.
a) Accepted Configuration-
Accept configuration rules are used to import ONLY the configurations that match the accept rule. Rest all other configurations, if being imported along with this DP, will be ignored and will NOT be imported. As an example, let us assume we want to import ONLY a crypto cert named, myCert.
We would need to provide exact configuration match corresponding to myCert.
It is a good practice to use match builder to write exact matching configuration.
Go to Accepted Configuration -> Build
A Match Builder dialog box appears where details need to be entered for an exact configuration path. The below six fields need to be filled –
· Device Address - Identifies the local management IP address of the device to which the statement is applied. Leave blank (or ‘*’) for all.
· Application Domain - Identifies the application domain to which the statement is applied. Select (none) for all.
· Resource Type – Identifies the name of the resource type, eg. Crypto certificate, web service proxy etc. To match all types, select '(all resources)'.
· Name Match (PCRE) - Limits the statement to resources with the specified names. Use a PCRE to select groups of resource instances. (PCRE refers to regular expression - eg. myCer*)
· Configuration Property- Limits the statement to the configuration property with the specified name.
· Configuration Value Match (PCRE) – Refers to configuration with matching property values. Use a PCRE Match Expression to select groups of configuration property values.
For this scenario, where we need only myCert to be imported from the entire set of objects, we would mention as below-
Since we need to import the entire myCert object, and not just a particular property, we would leave the last two options blank, as shown above.
Once we save, the below Accepted Configuration expression would be formed –
Next, Apply and save configuration.
This gives a Deployment Policy DPDemo which needs to be included along with imported object(s) to get only myCert imported during importing configuration.
b) Filtered Configuration –
In case when certain objects/configurations need to be filtered out during import, this property would be used. The configuration of Filtered Configuration expression is similar to the way we saw in Accepted Configuration. Kindly refer the process explained above (point a) for the same.
c) Modified Configuration –
As described above, Modified Configuration property would be used when the requirement is to change or modify certain properties/configurations in the imported object(s).
There is a separate tab for Modified Configuration.
As an example, suppose the requirement is to change the port number of the Front Side Handler (myFSH) getting imported from a different domain or environment.
Let the existing port number be 4788 and it needs to be changed to 4789.
Following steps would be followed to get the correct expression:
1. Go to Modified Configuration tab and click Add.
2. Go to Build to create a proper configuration match expression. Make the below entry –
The entry made, shows the existing FSH property that needs to be changed. Save the changes. The resultant expression is : */*/protocol/http?Name=myFSH&Property=LocalPort&Value=4788
3. Next, in Modification Type, there are three options –
· Add Configuration- To add a new property to the existing configuration
· Change Configuration- To change an existing configuration
· Delete Configuration- To delete an existing configuration
Here, in this example we need to change the existing configuration. So we follow the below steps. (In case one needs to add or delete, similar steps need to be followed. The options are self-explanatory.)
Next, Apply.
The below expression is formed. Apply and Save.
*/*/protocol/http?Name=myFSH&Property=LocalPort&Value=4788
Thus we get a new Deployment Policy DPDemo which should be included in the imported configuration to get the desired change.